Privacy & EU GDPR
In this module, we review the main goals and objectives of the new European Union General Data Protection Regulation (EU GDPR). 15:22 minutes
*Courses may vary.
Search Courses


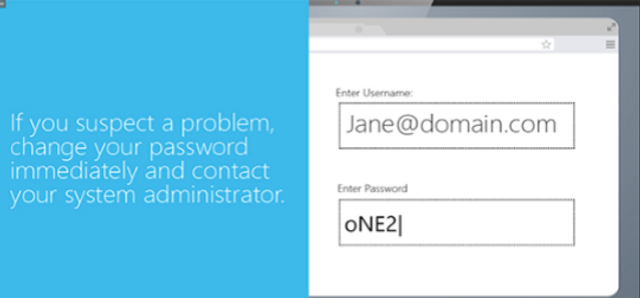
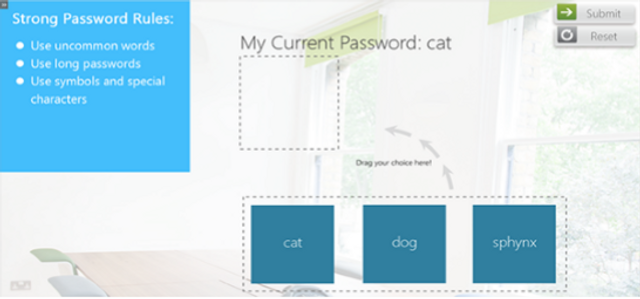












This interactive module defines malware in common terms, details the dangers it poses to organizations, and discusses preventative actions.
17:01 minutes





This security awareness module explains why top-level managers are targeted by malicious hackers, details common attack methods, and offers recommendations for avoiding security risks.
9:45 minutes


Please complete and submit the form below.