Password Security Brief
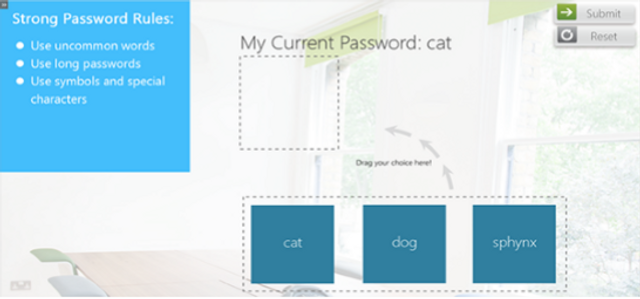
This module will summarize the best practices associated with creating and managing strong passwords, how to safely store passwords and what to do if you suspect that a password has been compromised. 3:59 minutes