Training
Training Courses
Course Catalog
*Courses may vary.
Search Courses
This awareness module covers concepts and best practices related to ensuring devices are configured securely. 8:49 minutes
Security Misconfiguration
In this module, we define security misconfiguration and offer tips on improving server security. 3:29 minutes

Using Components with Known Vulnerabilities
This module discusses use of components with known vulnerabilities that may undermine application defenses and enable various attacks. 3:29 minutes

Vulnerability Management
This awareness module covers identification and remediation of security vulnerabilities. 5:35 minutes
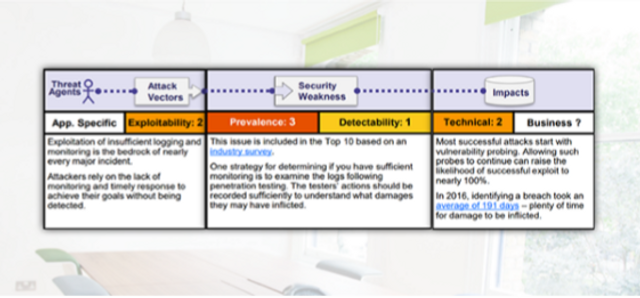
OWASP A10 - Insufficient Logging and Monitoring
This module covers insufficient logging and monitoring. 3:48 minutes

OWASP A6 - Security Misconfiguration
This module covers security misconfigurations. 4:04 minutes

OWASP A9 - Using Components with Known Vulnerabilities
This module covers using components with known vulnerabilities. 4:21 minutes

Check (Automatic Updates)
This micro-learning module highlights the importance of enabling automatic updates.
0:35 minutes

Insufficient Logging and Monitoring
Server administrators should maintain robust logs of activity on their servers. This module covers the risks associated with improper monitoring. 3:27 minutes

Insufficient Attack Protection
In this module, we’ll discuss web-application requirements regarding detection, prevention and response to both manual and automated attacks. 2:44 minutes

Malware for Executives
Executives are often targeted by hackers via malware, or malicious software. This module explains malware risks in detail and outlines steps executives can take to proactively keep their data secure. 7:23 minutes

Security Awareness for IT Professionals
This module explains fundamental concepts of information security and the important role IT professionals play in protecting organizational data assets. 10:37 minutes

Malware for Managers
This module will help managers understand the risks of malware, how to prevent installation and provide guidance on how managers can help their team and comply with internal security policies. 8:41 minutes

Protecting Mobile Devices (Video)
This video covers the steps you can take to protect your device from prying eyes and theft. Topics include screen locks, encryption and frequent software and firmware updates. 1:17 minutes

Where Is Your Device? (Backups)
This 60-second video details the importance of physical security and frequent data backups. 1:00 minutes
Mobile Security for Managers
This module will explain the risks of mobile devices and public networks in detail, and provide guidance on how managers can work with their teams to keep sensitive data secure. 7:03 minutes
Mobile Security for Executives
In this module, we review the risks of conducting business on mobile devices and public networks, and share best practices for working remotely at home and abroad. 6:05 minutes

H@ckj0b Season 1 Episode 1 “Recon”
h@ckj0b is your security team’s worst nightmare come to life. Will TechniCorp Dynamix survive Vermintooth’s assault, or will Tim leave them to deal with the mess they’ve gotten themselves into? 5:28 minutes
Check Yourself (BEC)
This module emphasizes the need to verify wire transfers.
1:00 minutes

Every Step You Take (Mentoring)
After you’ve learned good security practices, you should share your knowledge with others.
0:35 minutes

Knowledge Is Power (Security Training)
Security training should be a part of your daily life. 0:35 minutes

Double Check (Verifying Wire Transfers)
This micro-learning module emphasizes the importance of verifying wire transfers.
0:35 minutes
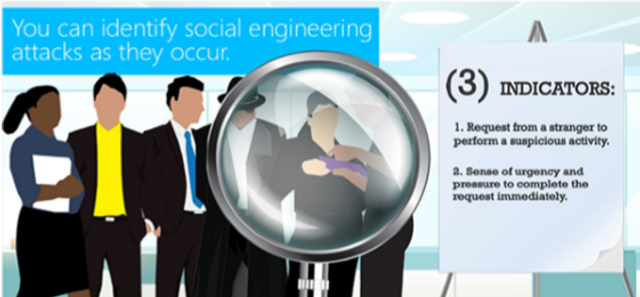
Identifying Social Engineering (Video)
This brief overview covers the hallmarks of social engineering attacks and how to prevent them. 1:29 minutes
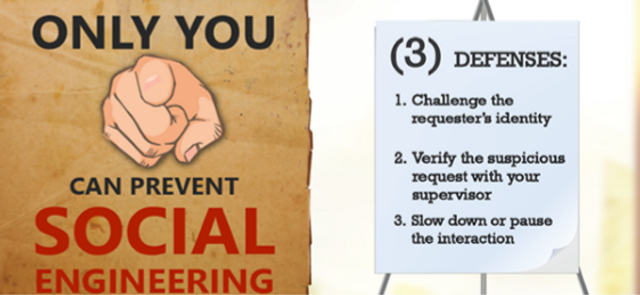
Social Engineering Defenses (Video)
This brief video shows you how to recognize and prevent social engineering attacks. 1:31 minutes

GDPR for Data Processors
This security awareness training covers privacy and EU General Data Protection Regulation for data processors.
11:08 minutes
GDPR for Managers
This security awareness training covers Privacy and the General Data Protection Regulation for Executives.
14:53 minutes

Request your free demo today.
Please complete and submit the form below.