WORKed Episode 7: Laptop Down
We’ve got a situation. Well, they do. Show your employees the importance of device security with this WORKed training module. 2:19 minutes
*Courses may vary.
Search Courses










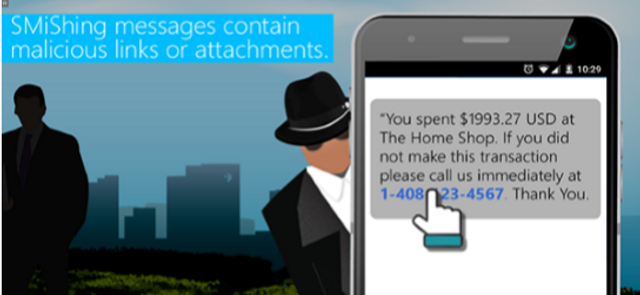
Spearphishing occurs when phishing messages are tailored for targeted individuals. This interactive module will help teams identify and avoid spearphishing attempts.
2:40 minutes












Please complete and submit the form below.