Conclusion
This module will review critical lessons from your security awareness training to increase team retention of core program content.
2:05 minutes
*Courses may vary.
Search Courses

This module will review critical lessons from your security awareness training to increase team retention of core program content.
2:05 minutes
The module will outline cyber threats (established and emerging), recent attacks and industry regulations, and also position employees as key players in modern cybersecurity initiatives.
5:13 minutes


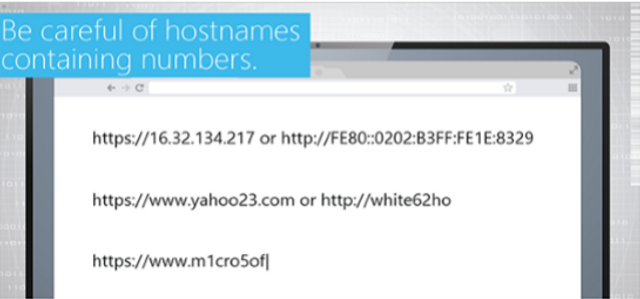
Spearphishing occurs when phishing messages are tailored for targeted individuals. This interactive module will help teams identify and avoid spearphishing attempts.
2:40 minutes




Ransomware is malware that holds technology for ransom. This module will show learners how ransomware works, what do if an infection occurs, and how to avoid future infections.
4:38 minutes


This module focuses on three key ways to prevent malware infections, details common sources of malware infections and discusses methods to help users avoid unsafe files.
3:21 minutes

This interactive module defines malware in common terms, details the dangers it poses to organizations, and discusses preventative actions.
17:01 minutes
Insider threats include security threats posed by employees, contractors or vendors. This module provides examples of common behaviors that can be indicators of insider threats.
3:46 minutes

Injection is one of the most common, and harmful, security risks to web applications. This module details different types of injection and suggests effective mitigation strategies for the workplace.
4:25 minutes

This module explains the encryption process and types of assets that can be encrypted and reinforces the importance of following encryption-related policies to protect sensitive information.
6:14 minutes

Cross-site scripting (XXS) allows attackers to run scripts in a victim’s browser to bypass access controls. In this module, we explain three types of XSS attacks and suggest XXS prevention measures.
3:35 minutes
In this module, we’ll review common exploitation techniques and ways learners can protect applications from cross-site request forgery.
3:16 minutes
This module will define the cloud and different types of cloud services available, and explain the benefits and risks of cloud-based services.
6:53 minutes

This module describes what incorrect implementation of authentication and session management functions are, and explains how it can allow attackers to assume other users’ identities.
4:39 minutes

This module covers broken access control, types of attacks and how to prevent them.
3:00 minutes

This security awareness module explains why top-level managers are targeted by malicious hackers, details common attack methods, and offers recommendations for avoiding security risks.
9:45 minutes

Please complete and submit the form below.