PCI DSS
This module details the training, policies and procedures required for Payment Card Industry Security Standard (PCI-DSS) compliance for handling branded credit cards from major vendors.
21:43 minutes
*Courses may vary.
Search Courses

This module details the training, policies and procedures required for Payment Card Industry Security Standard (PCI-DSS) compliance for handling branded credit cards from major vendors.
21:43 minutes

This one-minute video shows the consequences of a phishing attack.
1:00 minutes

Sometimes, trouble follows you home. Join in as Anthony and Ben explore the dangers of working remotely — from password cracks to malware attacks.
3:20 minutes

Some hackers don’t need computers at all. Join Anthony and Erica in exploring the dirty business of social engineering — when all it takes is a lie to crack open a company.
4:05 minutes

It’s a jungle in there. Explore the winding paths of the internet with Anthony and Cecil as they venture into thorny areas like fake browser warnings, HTTPS and dangerous URLs.
3:54 minutes

Can a thumb drive topple a company? It’s more likely than you think. Join Anthony and Harold as they check out the dangers of removable media — the good, the bait and the ugly.
2:52 minutes

Anthony and his pal Harold talk physical security. Why do you secure everything (even the printer), and what could someone get by sneaking in? Here’s how not to leave security out in the cold.
4:15 minutes

Learn how to spot the bait as Anthony guides his friend Cecil through the dangers of phishing. Is this actually a very exciting email from the boss, or is it just another hacker’s trap?
4:40 minutes

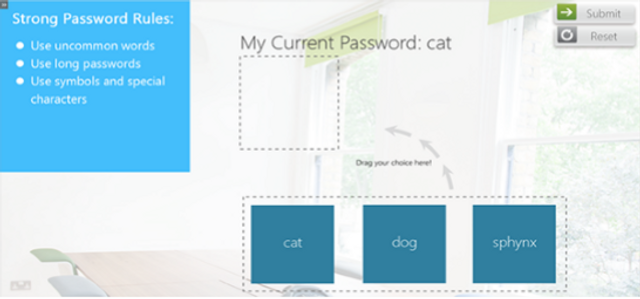
A system is only as secure as its password. Join Anthony and Daryl as they get to grips with the challenges of creating a strong password … because safety is not as easy as 1-2-3.
3:51 minutes

Join Anthony and Ivana as they explore the ups and downs of phone security. What is encryption? What kind of damage could a stolen phone do? Learn how to take security with you wherever you go.
3:32 minutes
Trojan horses, worms, RATs — There’s a whole animal kingdom of malware out there. Join Anthony and Fiona as they explore the best ways to keep malware from migrating into your system.
3:50 minutes
Take a moment to relax and review what you’ve learned as Anthony takes you through a few simple cybersecurity principles. Congratulations on completing your training!
2:25 minutes

Begin at the beginning as Anthony introduces you to our plan for what’s to come. Let’s talk about hackers, cybersecurity, and why it pays to keep a good head on your shoulders.
1:44 minutes

Our Mobile Wi-Fi Security module explains how to safely use wireless devices when operating on Wi-Fi connections.
2:07 minutes

This module focuses on three key ways to prevent malware infections, details common sources of malware infections and discusses methods to help users avoid unsafe files.
3:21 minutes

This interactive module defines malware in common terms, details the dangers it poses to organizations, and discusses preventative actions.
17:01 minutes

This short video reinforces the importance of using trusted publishers when installing mobile applications.
1:00 minutes
This security awareness module introduces common information security risks found when traveling abroad.
7:38 minutes

This module defines Intelligent Personal Assistants and how they work, and explains some of the risks associated with using intelligent personal assistants in the workplace.
8:14 minutes
This interactive module discusses security risks related to Internet of Things (IoT), how connected devices may be attacked, and steps for safe use of IoT.
5:35 minutes
Insider threats include security threats posed by employees, contractors or vendors. This module provides examples of common behaviors that can be indicators of insider threats.
3:46 minutes

Injection is one of the most common, and harmful, security risks to web applications. This module details different types of injection and suggests effective mitigation strategies for the workplace.
4:25 minutes

In just one minute, this video explains the risks of connecting to public Wi-Fi networks, including how sensitive information can be intercepted by attackers.
1:00 minutes

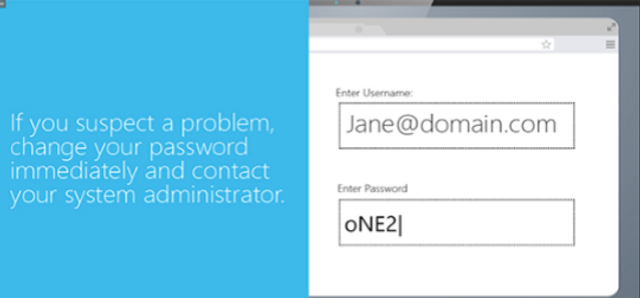
In less than one minute, this video reinforces the importance of keeping passwords private.
1:00 minutes

Please complete and submit the form below.