Training
Training Courses
Course Catalog
*Courses may vary.
Search Courses

Physical Security and PHI
HIPAA includes specific requirements for physical safeguards that every organization should have in place to secure protected health information (PHI).
10:19 minutes

Physical Security for Executives

Data Retention
This module walks learners through common data retention plans, data types typically subject to data retention policies and secure data disposal considerations.
4:32 minutes
Data Destruction
This module reinforces the importance of secure data-disposal methods and shares best practices for disposal of sensitive data.
2:17 minutes

Software Licensing (Video)

EAL Malware
This module teaches learners how to avoid falling victim to malware.
1:46 minutes

Appropriate Use of Software (Video)
In less than 60 seconds, this module covers how to legally use products of creative software.
0:58 minutes

Intellectual Property
This module covers important intellectual property protection mechanisms (patents, trademarks, and copyrights) and how they apply to various types of products, including software and digital media.
5:38 minutes
Intellectual Property Rights (Video)
This video covers the basics of US copyright and trademark laws.
1:45 minutes

Antivirus (Video)
This video details the threats antivirus software can and cannot mitigate.
0:47 minutes

Updates And Patches (Video)

Secure Configuration
This awareness module covers concepts and best practices related to ensuring devices are configured securely.
8:49 minutes
Security Misconfiguration
In this module, we define security misconfiguration and offer tips on improving server security.
3:29 minutes

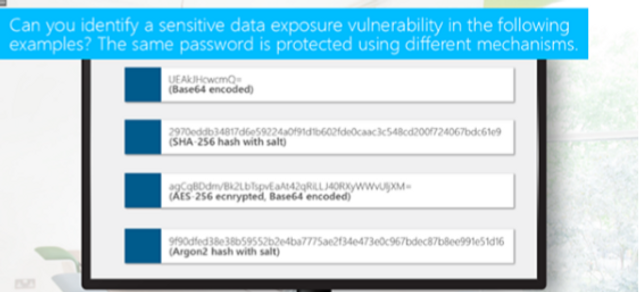
Using Components with Known Vulnerabilities

Vulnerability Management
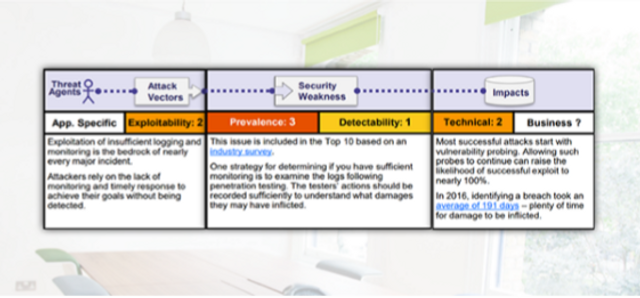
OWASP A10 - Insufficient Logging and Monitoring
This module covers insufficient logging and monitoring.
3:48 minutes

OWASP A9 - Using Components with Known Vulnerabilities
This module covers using components with known vulnerabilities.
4:21 minutes

OWASP A6 - Security Misconfiguration
This module covers security misconfigurations.
4:04 minutes

Check (Automatic Updates)
This micro-learning module highlights the importance of enabling automatic updates.
0:35 minutes

Insufficient Attack Protection
In this module, we’ll discuss web-application requirements regarding detection, prevention and response to both manual and automated attacks.
2:44 minutes

Insufficient Logging and Monitoring
Server administrators should maintain robust logs of activity on their servers. This module covers the risks associated with improper monitoring.
3:27 minutes

Ransomware and HIPAA

Malware for Educators
This interactive module defines malware and details the dangers it poses to educational institutions, as well as preventative actions.
7:15 minutes
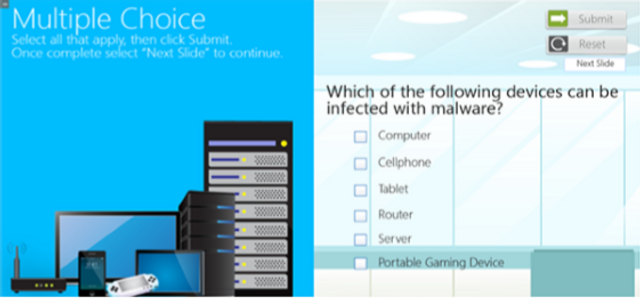
Malware for Financial Institutions
This interactive module covers malware and the dangers it poses to financial organizations as well as preventative actions.
8:04 minutes

Malware and PHI for Executives
This training outlines steps healthcare executives can take to proactively keep PHI secure. Suggested security policies and staff communication strategies are also introduced in this module.
9:11 minutes

Request your free demo today.
Please complete and submit the form below.